
The Unseen Perils of Social Media to Your Business: A Darkhorse Dental IT Insight️
Ever considered your business might be tiptoeing into the invisible web of social media dangers? Has the idea of potential cyber threats linked with your social media use crossed your mind? Social media, once a basic tool for interaction, has now become a potential gateway for cyber breaches. Your business reputation, customer data privacy, your valuable information, and even your team's safety might be at stake. It's critical for business operators and stakeholders to comprehend the weight of a well-thought-out social media strategy reinforced by robust cybersecurity measures.
Inthis Darkhorse Dental IT blog, we plunge into the cyber risks tied to socialmedia usage and chart a course for the precautions your business and employeesneed to undertake to combat them.
The Perils of Social Media in the Cybersecurity Landscape️Social media has intertwined into our daily lives in the digital era. From sharing memorable snaps and side-splitting memes to connecting with loved ones around the world , social media has revolutionized communication. Yet, with each passing year, the cybersecurity risks linked to these accounts swell. Cybercriminals zero in on these platforms, and in the wrong hands, your personal and business details could fuel illegal activities.
The malicious acts range from data mining, social engineering attacks that target employees' personal accounts or company information on public platforms, phishing scams poised to filch confidential data or funds, and reputation damage caused by misinformation spread.

So, remember to be careful about the information you share on social media and take measures to guard your business against these lurking threats.
Data Mining In essence, social media was designed to be social. Thus, it's an information sharing freeway and one where cybercriminals are speeding in the fast lane. As data is shared on social media, the criminals in the shadows are mining this data.
Datamining extracts valuable insights from extensive datasets, uncovering hidden patterns, connections, and trends. While businesses employ this tool to gain customer insight and market share knowledge, cybercriminals exploit it to collect data from various platforms, laying the groundwork for disaster. Everything is fair game - family details, personal interests, and even insight that might lead to cracking a sensitive password.
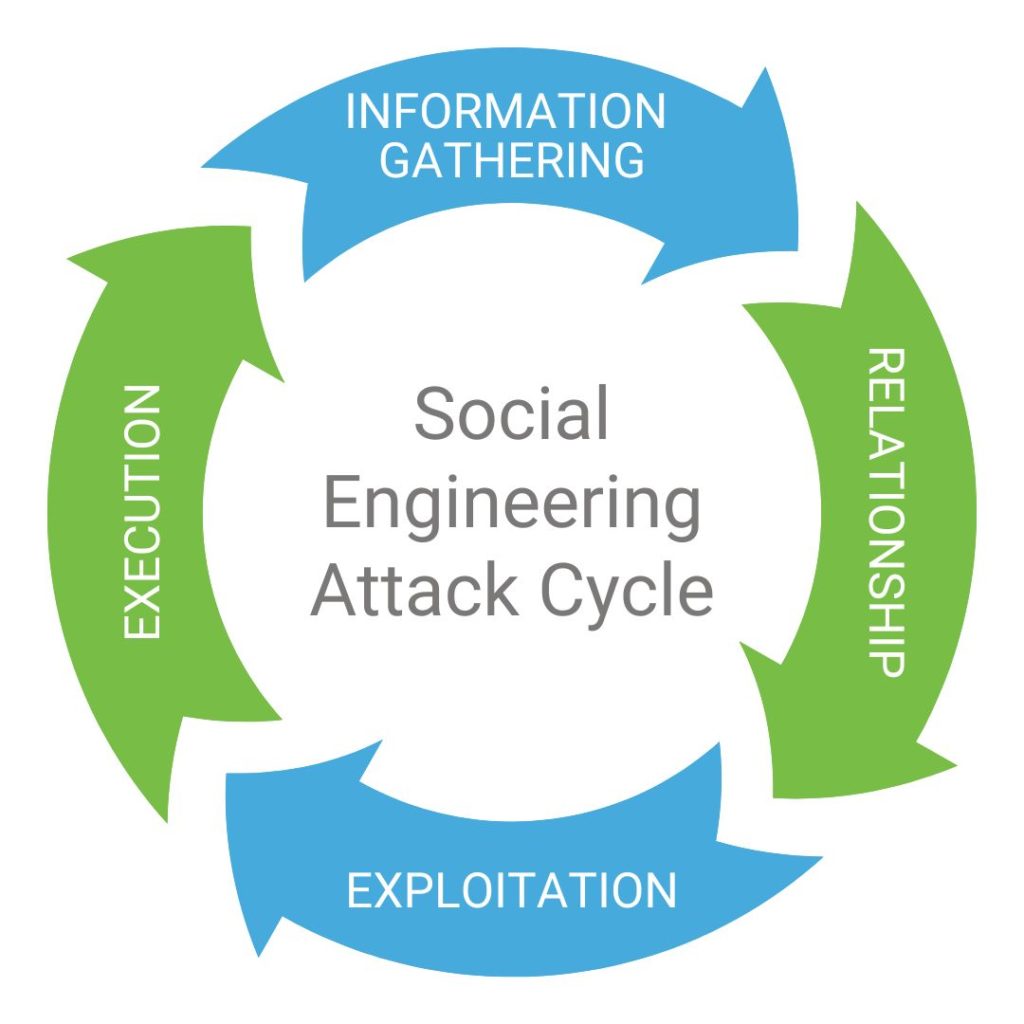
Social EngineeringSocial engineering is the crafty technique cybercriminals use to earn their targets' trust, luring them to drop their guard and spill sensitive information. The tactics range from manipulating individuals into downloading malicious software, visiting hoax websites, transferring money to criminals, and falling prey to other errors compromising personal or business security.

Beingable to spot the red flags of social engineering can safeguard you and yourteam from becoming victims:
- Panic-inducing requests
- Unsolicited help or information
- An offer that seems too good to be true
- A strange message from a 'trusted source'
- Unusual communication from a friend or family member (like your mom sending an email at 3 am )
- An unverified sender ️ Infographic highlighting the red flags of social engineering.
Phishing ScamsPhishing scams are devious ploys by cybercriminals to access usernames, passwords, financial data, or other confidential information. The criminal typically tries these tricks through channels like email spoofing, malware-ridden websites, or malicious links sent via text message. Recognizing the signs of phishing scams and defending your customers and employees from such attacks is essential.
Reputation Damage Your business reputation is invaluable. You toil to build a business that you, your team, and your customers (present and future) can take pride in. Protecting that reputation is crucial. Social media could expose your business to reputation damage risks due to misinformation or harmful actors.
Cybercriminals see your social media presence as a goldmine of information ripe for impersonation. Creating phony accounts, making purchases in your name, locking you out of accounts, or extracting additional information from your associates– all these are tactics cybercriminals use to tarnish your business's reputation.
Stay Safe on Social Media: Best Practices for Businesses and Employees In the digital age, it's vital for businesses to acknowledge the risks that come with social media. As a business owner or an employee, be proactive in safeguarding your valuable assets. To assist in this mission, we've put together some best practices for the business and its employees to ensure secure and protected social media usage.
Best Practices for Businesses Using Social Media In truth, social media is the lifeblood of any business today. As much as it breathes life into your brand, it also brings potential security risks. But, fear not; we've got your back. Here are some best practices to keep your social media accounts secure:
- Conduct thorough background checks on anyone with page access
- Use secure passwords and enable two-factor authentication (2FA)
- Limit the number of page administrators
- Monitor all company public accounts for potential threats or harmful activity
- Organize employee cybersecurity training covering social media usage and other digital tools.
Best Practices for Employees Using Social Media Social media offers another channel to communicate and connect with family, friends, coworkers, and brands. But it also poses a significant risk for individuals and businesses alike. Employees need to be aware of social media risks and take steps to protect their personal information and the company's assets. Here are some best practices for employees when using social media:
- Use secure passwords and enable two-factor authentication (2FA)
- Refrain from sharing confidential information
- Regularly check account privacy settings to ensure only trusted individuals have access to your data
- Avoid sharing work information
- Be cautious of fake accounts
- Steer clear of quizzes, too-good-to-be-true offers, donation requests, and suspicious follow requests
️Shielding Your Business from Cyberattacks️ In the current digital landscape, cybersecurity isn't a luxury, but a necessity. Security Magazine reports that over 2,200 cyberattacks happen daily – which totals to over 800,000 each year. Plus, over 600,000 Facebook accounts are hacked every day. With the increase in phishing scams and malware threats, protective measures are essential.
Start with a comprehensive network security solution to protect your vital business data. This should encompass intrusion detection systems, firewalls, and encryption. Implement ongoing cybersecurity training for your employees, covering best practices for social media use. Lastly, conduct regular assessments of your IT infrastructure to spot potential weak areas.
Remember Benjamin Franklin's wise words, "An ounce of prevention is worth a pound of cure." Shield your business from the ever-adapting world of cyberthreats, and rest easy knowing your sensitive information is safe from harm.
Conclusion
In today's digital reality, cybersecurity is non-negotiable. From data mining, social engineering, phishing scams, to reputation damage, the threats posed by cybercriminals
Related Articles:
-Revamping Tech for Business Success: 5 Perils of Using Outmoded Technology
-The Perils of Enlisting Friends and Family IT Support for Your Dental Practice
-Darkhorse Dental IT Presents: Is Moving to the Cloud Right for Your Dental Practice?
Darkhorse Dental IT Is Here For You
We understand that caring for your patients is your top priority. Dealing with a computer issue, slow IT response time or HIPAA compliance requirements just aren’t high on your list of to-do’s. That’s where Darkhorse Dental Tech comes in. Our team of Dental IT specialists are experts when it comes to running a great, secure and successful practice —and so much more. Whether you’re looking for IT services for startups, or existing support and security services for your practice, Darkhorse can do it all for you, so you can get back to your patients.
Have questions? Looking for ideas? Just want to talk teeth? Drop us a line at sales@darkhorsetech.com to get the conversation started! Or head to our Contact page to send us a message. Don’t forget to follow us on Instagram!
Dental IT Support, Dental Startups, Dental IT Support New York, Dental IT Support Texas, Dental IT Support North Carolina, Dental IT Support Raleigh, Dental IT Support Charlotte, Dental IT Support Wake Forest, Dental IT Support Florida, Dental IT Support California, Dental IT Support Pennsylvania, Dental IT Support New Jersey, Cloud Dental Solutions, Dental Technology.
.svg)
